UCX Suite HD Drive Encryption with Bitlocker
This KB article applies to Imagicle UCX on-prem Suite owners. If your Imagicle UCX Suite is deployed in the Cloud, the hard disk encryption is applied in AWS Data Centers, compliant with ANSI/TIA-942 Tier 4.
Introduction
A secure computing environment would not be complete without consideration of encryption technology. This article describes how it is possible to encrypt Imagicle UCX Suite server storage leveraging Microsoft BitLocker feature.
BitLocker is Microsoft's encryption program that provides full-disk encryption of the hard drives. By utilizing the latest encryption algorithms and leveraging the power and efficiency of modern CPUs, the entire contents of the startup disk are encrypted, preventing unauthorized access to the data stored on the disk, save for those with either the login account to decrypt the disk, or those which possess the recovery key.
By enabling BitLocker's whole-disk encryption, data is secured from prying eyes and all attempts to access this data physically or over the network will be met with either prompts to authenticate or error messages stating the data cannot be accessed even when attempting to access data backups, as BitLocker encrypts those too.
Configuration
Adding (virtual) floppy drive
For the sake of simplicity, in this article the encryption key will be stored on the floppy drive. Make sure floppy resource is configured in your environment and, if not, follow the below steps to make it available into a VSphere environment.
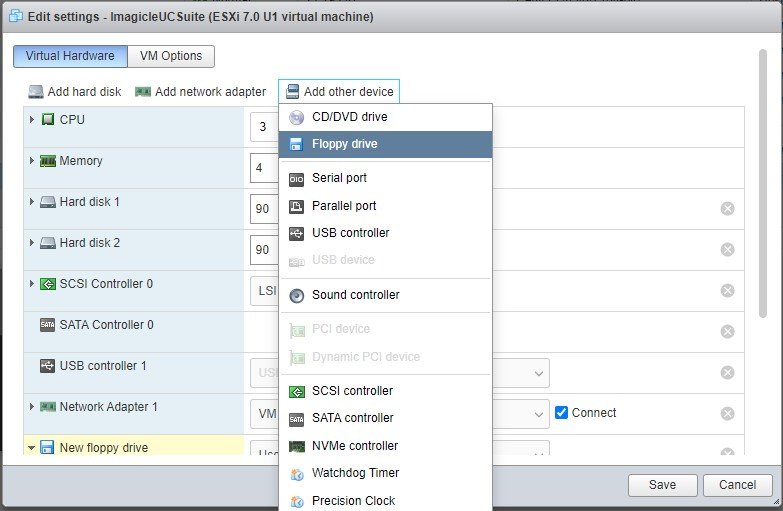
Click on "Add other device" and then on "Floppy drive"
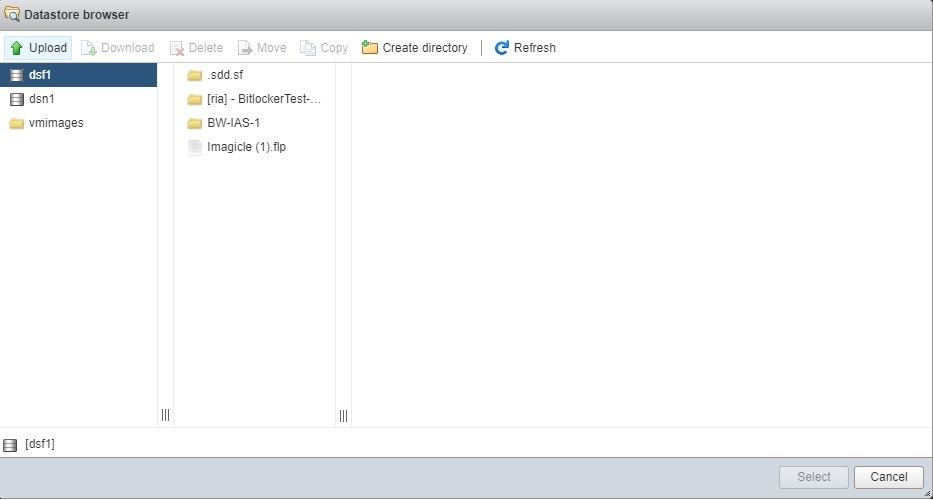
Download this following floppy file, and upload it to the desired data store as shown below:
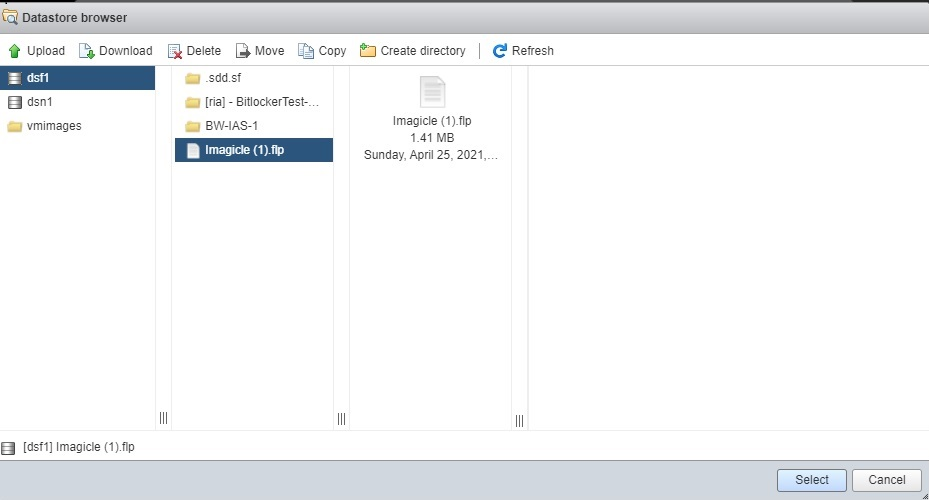
Select the uploaded file and click on "Select"
A new floppy drive will appear as follows:
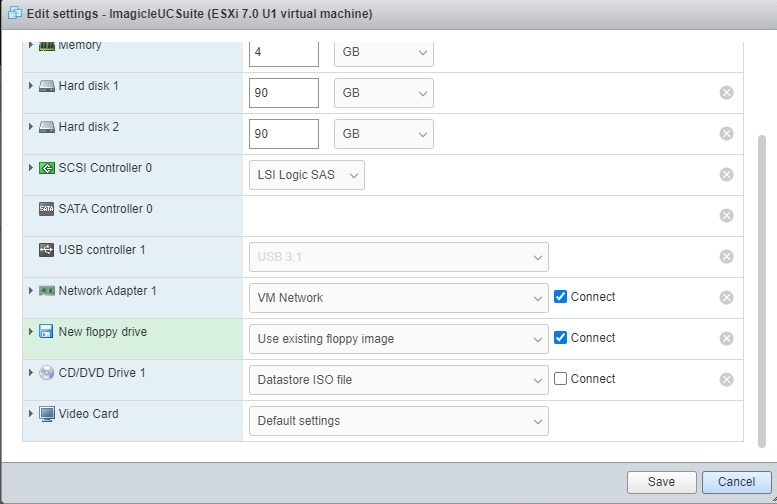
Make sure that the "Connect" checkbox is enabled on the added drive.
Enabling Bitlocker
Access Imagicle UCX Suite server through a Remote Desktop session and launch Server Management.
Click on "Add Roles and Features" and, within the wizard, please select "Features" from left pane.
Then click on "Enhanced Storage" and "BitLocker Drive Encryption". See below.
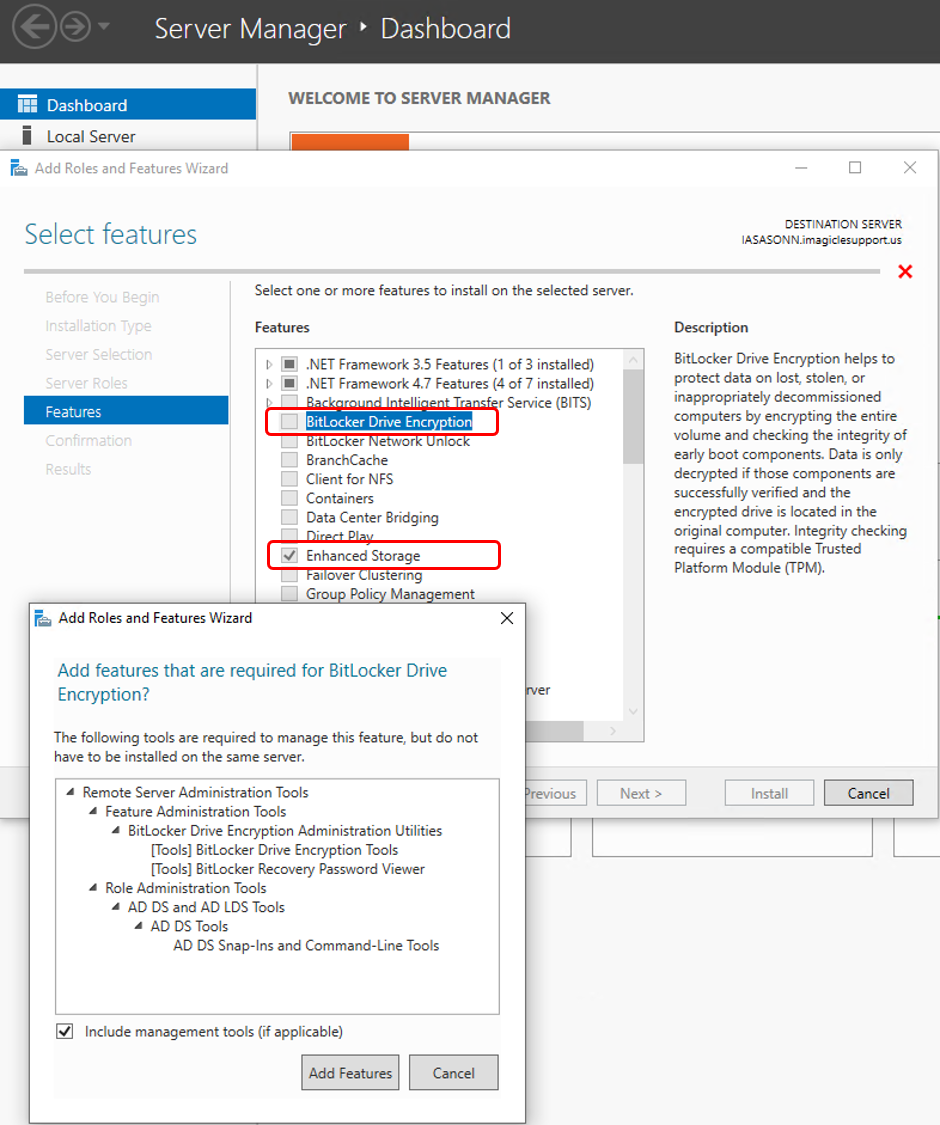
Complete the wizard and then reboot Imagicle VM. More info available here .
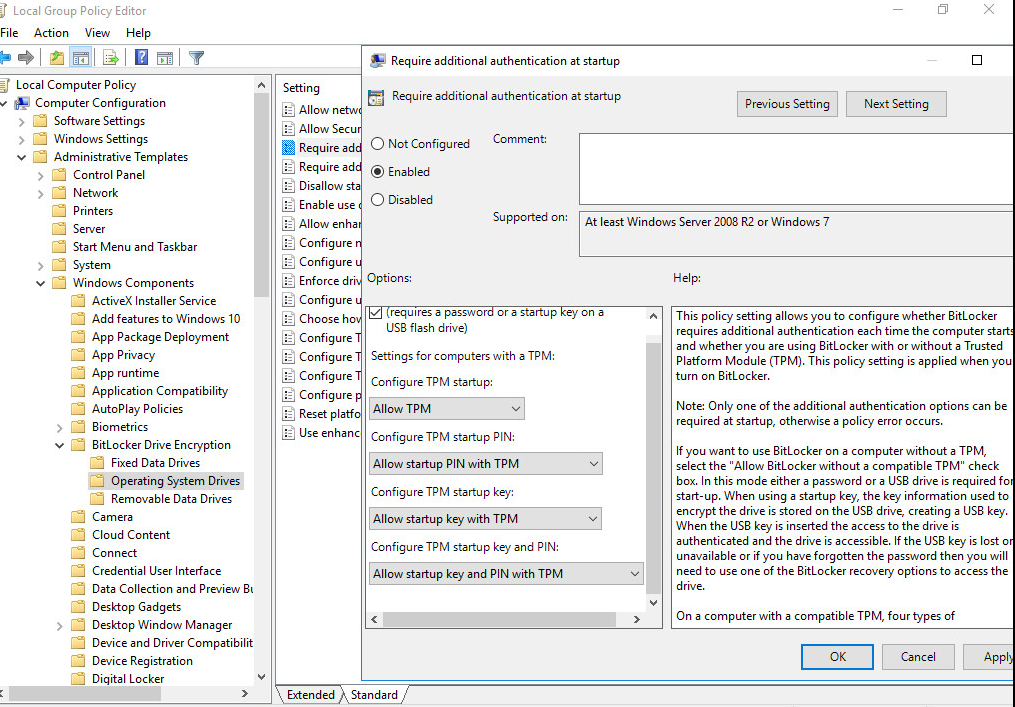
Once rebooted, please access to Local Group Policy Editor (gpedit.msc) and navigate to "Require additional authentication at startup", as described in picture below. Select "Enable". Make sure the other options are as in picture below. Click on "Apply" and "OK". Close Local Group Policy Editor.
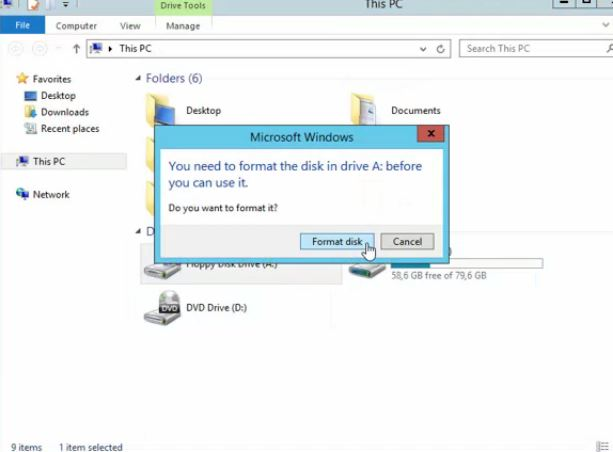
Select in the VM the created floppy drive and format it with default settings.
Generating and saving the Encryption key
From the VM that needs to be encrypted, open a CMD prompt window as admin and navigate to C:\windows\system32\
Run the command manage-bde.exe –on C: -rp –sk A: ("A" represents the floppy drive. the letter might be different)
This command generates a key (i.e. 068552-159588-193347-063712-370997-614405-340516-XXXXXX), and saves it in the floppy drive. The floppy drive provides the key at each boot, enabling the VM to properly boot.
It is very important to save the generated key in a safe place, in case the virtual floppy content is lost (i.e. damaged, unreadable, ...). Please copy it from the prompt windows to a text file and store it in a safe place, as it contains the key enabling boot of the whole virtual server.
Check that Hard Drive is set to be first in order, reboot the VM and wait a few time until encryption process starts, as shown in picture below.

Final Recommendations
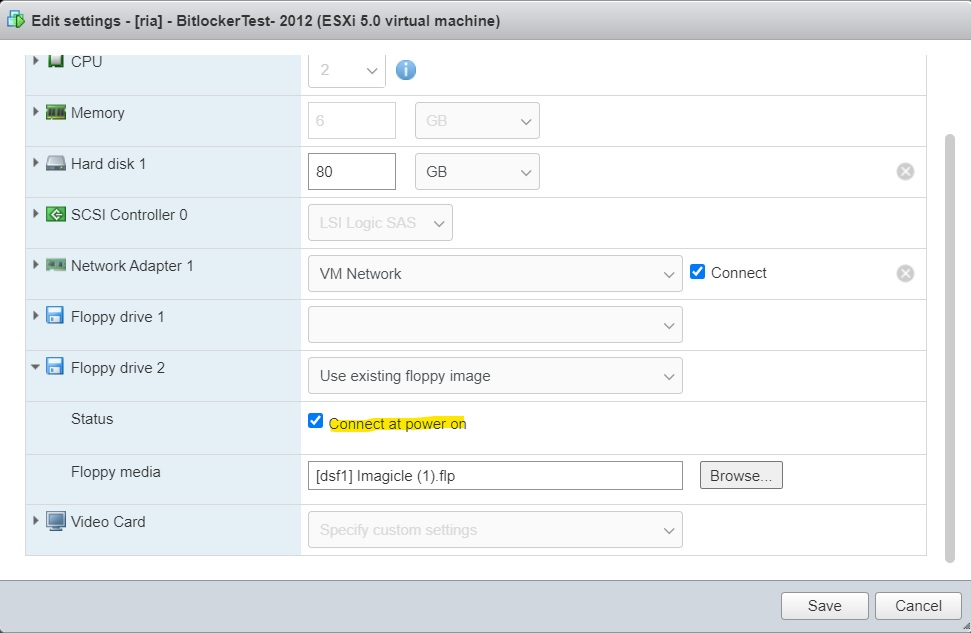
Make sure the VM properties are configured as reported in the following picture; enabling the flag "Connect at power on" makes the floppy (with the key that is installed into it in the next steps) available at boot time.
Make also sure VM boot order in the BIOS has hard Drive in first place (prior to any other I/O devices)
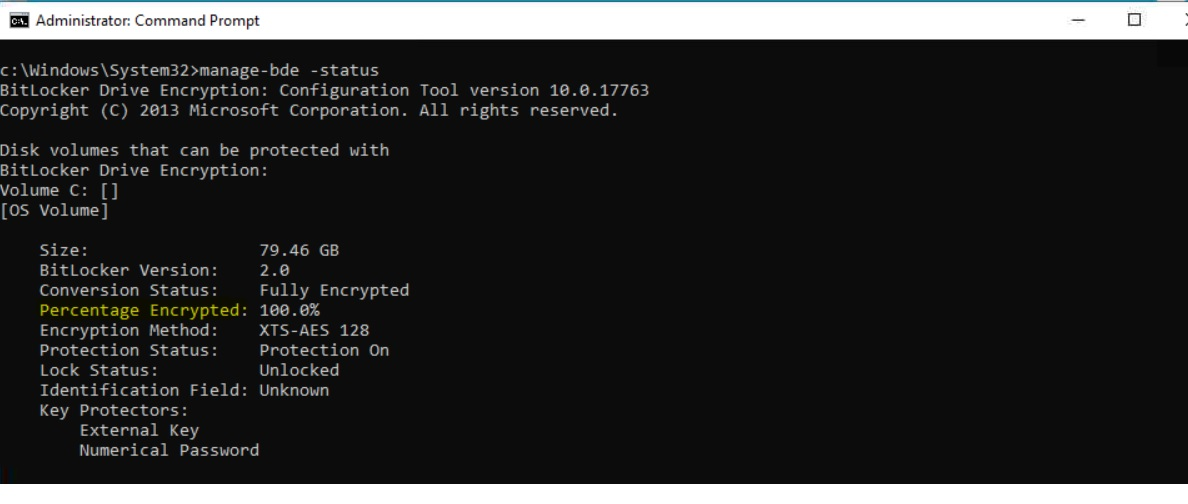
To verify that the encryption is fully completed, please run the following command on the CLI:
manage-bde -status
If a VMware snapshot of the Imagicle virtual server has been taken before disk encryption, please take into consideration the below points:
Be aware the encryption process will be significantly slower;
Ensure you have enough available space in the VMware datastore hosting the Imagicle virtual server, roughly twice the size of the virtual disk size being encrypted.
